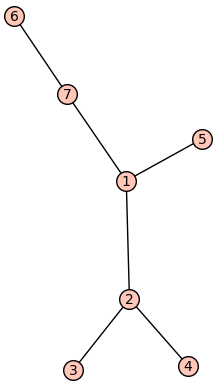
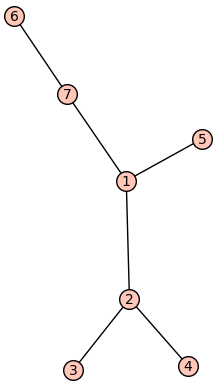
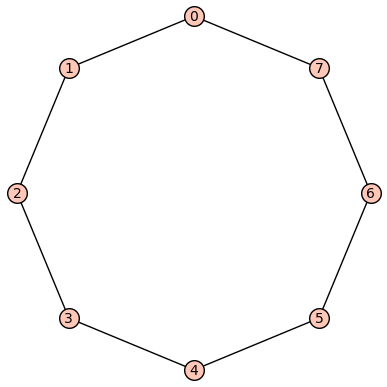
Definition 3.5.1.
Given a finite connected graph \(G\text{,}\) a spanning tree of \(G\) is a tree \(T\) on the same vertex set as \(G\) where the edge set of \(T\) is contained in the edge set of \(G\text{,}\) i.e., \(E(T)\subseteq E(G)\text{.}\)
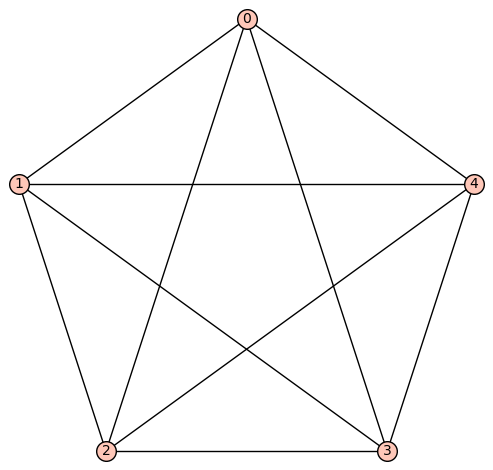
https://oeis.org/A000272.